Home / Cybersecurity Best Practices for Businesses in 2026: A Complete Protection Guide
Cybersecurity Best Practices for Businesses in 2026: A Complete Protection Guide
sarankk | March 1, 2026 | 18 min read
Table of Contents
Cybercriminals are no longer lone hackers in dark basements. In 2026, they operate as sophisticated, well-funded organizations deploying artificial intelligence, automation, and social engineering at scale. From AI-generated phishing emails that mimic your CFO’s writing style to ransomware attacks that bring entire hospital networks to their knees in minutes — the cyber threat landscape has evolved faster than most businesses can keep pace.
The consequences are no longer abstract. The average cost of a data breach reached $4.9 million in 2024, and projections for 2026 push that figure even higher when factoring in regulatory fines, reputational damage, and operational downtime. No business — whether a 10-person startup or a Fortune 500 company — is immune.
The good news? Strong cybersecurity doesn’t require an unlimited budget. What it requires is strategy, consistency, and a culture of vigilance. This complete guide walks you through the most critical cybersecurity best practices for businesses in 2026 — covering everything from identity management and cloud security to incident response planning and emerging AI-powered defenses. Whether you’re an IT manager, founder, or executive, this guide gives you the tools to protect what matters most.
The Cybersecurity Landscape in 2026

To defend against threats, you first need to understand them. The 2026 threat landscape is defined by speed, sophistication, and scale — powered in large part by the same AI tools businesses use to become more efficient.
AI-Powered Phishing & Deepfake Fraud
Generative AI now enables attackers to craft hyper-personalized phishing emails that reference real meetings, mimic writing styles, and even generate deepfake audio or video of executives instructing employees to transfer funds or share credentials. These Business Email Compromise (BEC) attacks are nearly indistinguishable from legitimate communications.
Ransomware-as-a-Service (RaaS)
Ransomware is no longer the exclusive domain of technically skilled hackers. Criminal platforms now operate like SaaS companies — offering ransomware toolkits, customer support, and even revenue-sharing models to affiliates. This has dramatically lowered the barrier to entry for cybercriminals and increased the frequency and diversity of attacks.
Cloud Security Risks
As more businesses shift critical workloads to the cloud, misconfigurations — exposed storage buckets, over-permissioned service accounts, insecure APIs — remain the leading cause of cloud data breaches. Cloud environments are powerful but complex, and gaps in configuration are constantly exploited.
Supply Chain Vulnerabilities
Attackers increasingly target third-party vendors and software suppliers to gain access to their real targets. A single compromised plugin, software update, or vendor access point can expose hundreds or thousands of downstream businesses simultaneously.
According to the Cybersecurity and Infrastructure Security Agency (CISA), supply chain attacks increased by over 300% between 2021 and 2024, with no signs of slowing in 2026. Understanding these vectors is the first step toward building a resilient defense.
Implement a Zero Trust Security Model
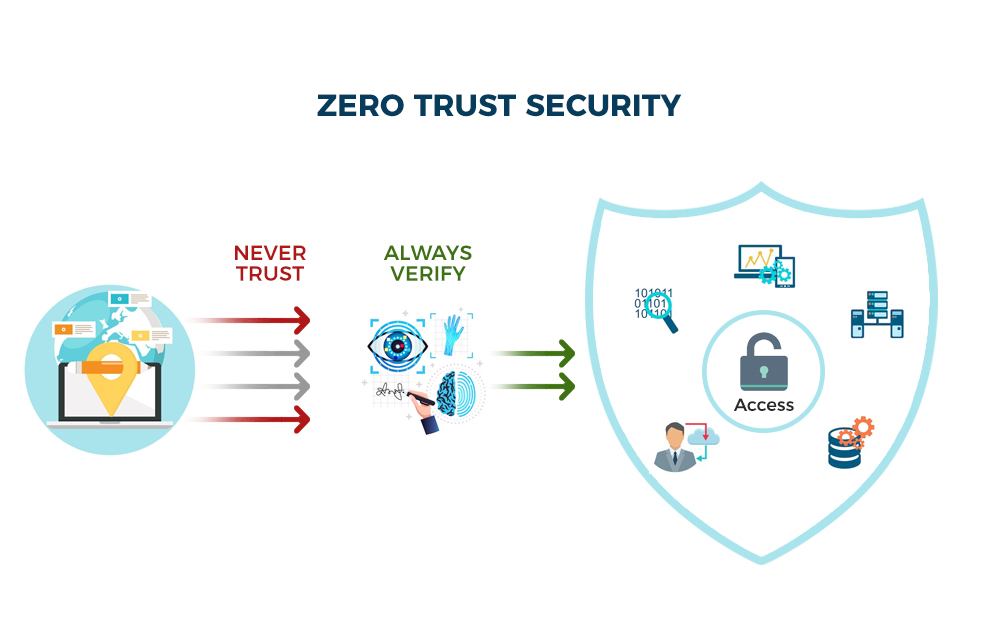
The traditional security model assumed that everything inside a corporate network could be trusted. Zero Trust obliterates that assumption. In a Zero Trust architecture, no user, device, or application — inside or outside the network — is automatically trusted. Every access request must be verified, every time.
“Never Trust, Always Verify”
This is the core principle. Even if a user has valid credentials, the system evaluates context: Is this device compliant? Is the login location unusual? Is this access pattern consistent with the user’s role? If anything seems off, access is denied or stepped up with additional authentication.
Identity Verification & Device Authentication
Every user must prove who they are (identity) and that their device meets security standards (device posture) before gaining access. This includes evaluating device health — Is the OS patched? Is antivirus active? Is encryption enabled?
Micro-Segmentation
Zero Trust architectures divide networks into small, isolated segments. Even if an attacker gains access to one segment, they cannot move laterally to other parts of the network. This dramatically limits the blast radius of any breach.
Benefits for Hybrid and Remote Teams
With remote and hybrid work now the norm, Zero Trust is especially critical. Employees accessing corporate resources from home networks, personal devices, or coffee shops represent significant risk vectors. Zero Trust ensures that location is never a substitute for identity verification.
Key platforms enabling Zero Trust in 2026 include Microsoft Entra ID, Zscaler, Cloudflare Access, and Google BeyondCorp Enterprise.
Strengthen Identity & Access Management (IAM)
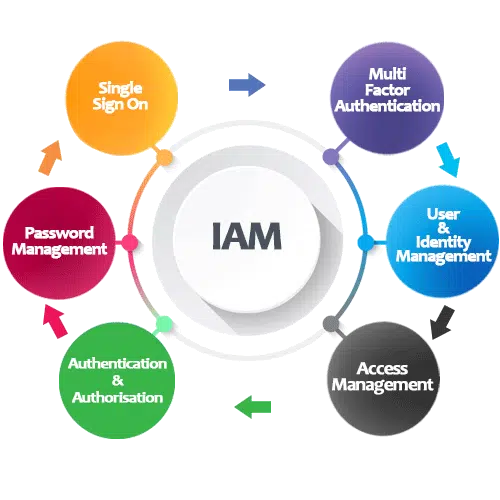
Compromised credentials are the single most common entry point for cyberattacks. Strengthening how your organization manages identities and access permissions is one of the highest-ROI security investments you can make.
Enforce MFA Across All Systems
Multi-factor authentication (MFA) requires users to verify their identity with at least two factors — typically something they know (password) and something they have (phone, hardware key). Microsoft reports that MFA blocks more than 99.9% of account compromise attacks. In 2026, MFA should be considered table stakes, not optional.
Prefer authenticator apps or hardware keys (FIDO2/WebAuthn) over SMS-based MFA, which remains vulnerable to SIM-swapping attacks.
Role-Based Access Control (RBAC)
Not every employee needs access to every system. RBAC ensures that users only access the data and applications their job role requires — nothing more. This principle of least privilege limits the damage that can be done if any single account is compromised.
Single Sign-On (SSO)
SSO platforms (like Okta, Microsoft Entra, or Google Workspace) streamline access while centrally enforcing security policies. Users log in once and gain access to all authorized apps — reducing password fatigue and the risk of reused or weak passwords across multiple systems.
Privileged Access Management (PAM)
Accounts with elevated privileges — IT admins, database administrators, finance leads — are prime targets for attackers. PAM solutions enforce strict controls, session recording, time-limited access, and just-in-time privilege elevation for these high-risk accounts.
Passwordless Authentication
The future of authentication is passwordless. Technologies like biometrics, passkeys, and hardware security keys eliminate the weakest link in your security chain. Major platforms including Apple, Google, and Microsoft are now aggressively pushing passwordless adoption
Secure Cloud Infrastructure & SaaS Applications
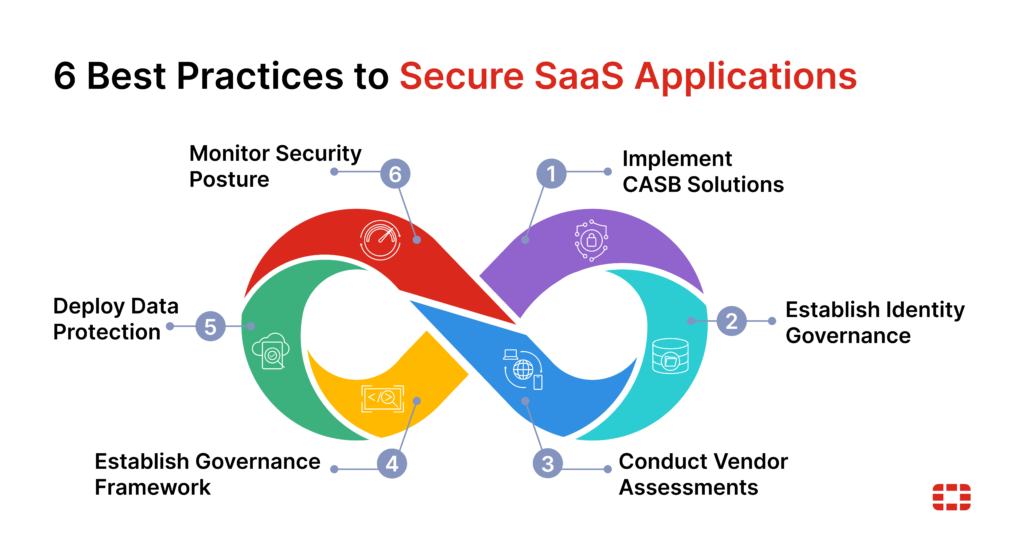
The cloud unlocks enormous flexibility and scalability — but it also introduces a complex web of security responsibilities. In 2026, businesses are operating in multi-cloud and hybrid environments, managing dozens of SaaS applications, often with limited visibility into who has access to what.
Misconfiguration Risks
The number-one cause of cloud breaches isn’t sophisticated hacking — it’s misconfiguration. Publicly exposed S3 buckets, overly permissive IAM roles, and open security groups can leave sensitive data accessible to anyone who knows where to look. Continuous configuration monitoring is non-negotiable.
Cloud Access Security Brokers (CASB)
CASB tools act as intermediaries between your users and cloud services, enforcing security policies, providing visibility into shadow IT (unauthorized SaaS use), and detecting anomalous behavior. Leading solutions include Microsoft Defender for Cloud Apps, Netskope, and Zscaler CASB.
Data Encryption — At Rest & In Transit
Encrypt all sensitive data both when it’s stored (at rest) and when it’s being transmitted (in transit). Use TLS 1.3 for data in transit and AES-256 for data at rest. Ensure your cloud provider offers encryption key management that gives you control — not just theirs.
The Shared Responsibility Model
Cloud providers like AWS, Azure, and Google Cloud secure the underlying infrastructure — but you are responsible for securing everything you put on top of it: your data, applications, identities, and configurations. Many breaches occur because businesses assume the cloud provider handles more than they actually do.
Monitor Cloud Workloads Continuously
Implement Cloud Security Posture Management (CSPM) tools to continuously scan your cloud environment for misconfigurations, compliance violations, and anomalies. Platforms like Prisma Cloud, Wiz, and AWS Security Hub provide real-time visibility across complex multi-cloud environments.
Protect Against Ransomware & Phishing Attacks
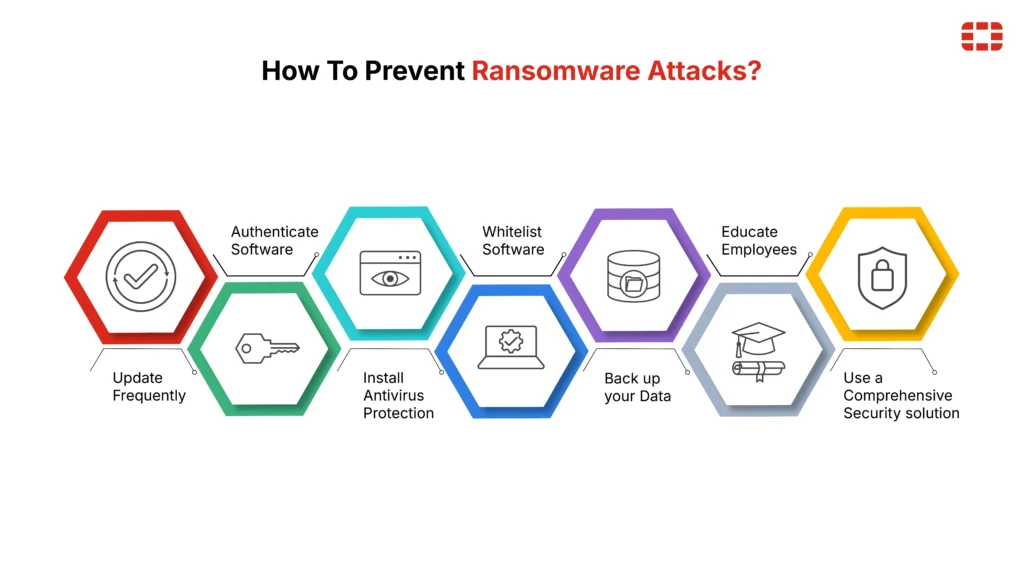
Ransomware and phishing remain the two most prevalent and damaging attack types in 2026. They often work together — phishing delivers the initial payload, ransomware delivers the damage. A layered defense addresses both.
Email Filtering & DMARC Policies
Your email gateway is your first line of defense. Deploy advanced email filtering with AI-powered threat detection to catch malicious attachments, suspicious links, and spoofed senders before they reach inboxes. Implement DMARC, DKIM, and SPF records to prevent attackers from spoofing your domain to target your employees or customers.
Endpoint Detection & Response (EDR)
Traditional antivirus is insufficient against modern threats. EDR solutions like CrowdStrike Falcon, SentinelOne, and Microsoft Defender for Endpoint continuously monitor endpoint activity, detect behavioral anomalies, and respond automatically to contain threats — often before human analysts are even alerted.
Regular Offline Backups
The most effective ransomware defense is a backup you can actually restore. Maintain multiple backup copies following the 3-2-1 rule: 3 copies of data, on 2 different media types, with 1 stored offline or air-gapped. Test your restoration process regularly — a backup you haven’t tested is a backup you can’t trust.
Employee Phishing Simulations
Human behavior is your biggest vulnerability and your biggest opportunity. Run regular, realistic phishing simulations to train employees to recognize and report suspicious emails. Track click rates and tailor training to your highest-risk groups.
Incident Containment Procedures
Speed matters when ransomware strikes. Pre-define containment procedures: isolate affected systems immediately, disable compromised accounts, and preserve forensic evidence before remediation begins. Having a playbook ready before an attack dramatically reduces response time and damage.
Employee Cybersecurity Training & Awareness

Technology alone cannot protect your business. According to IBM’s Cost of a Data Breach Report, human error is a contributing factor in over 95% of cybersecurity incidents. Your employees are simultaneously your greatest vulnerability and — when properly trained — your most powerful line of defense.
Build a Security-First Culture
Cybersecurity awareness must be baked into your organization’s culture, not treated as a once-a-year checkbox compliance activity. Leaders set the tone: when executives champion security practices, employees follow. Create an environment where reporting suspicious activity is encouraged and rewarded, never punished.
Regular Simulations & Workshops
Annual security training is not enough in 2026. Conduct monthly micro-training sessions, quarterly phishing simulations, and hands-on workshops covering real-world scenarios. Tailor content to role-specific risks — your finance team faces different threats than your engineering team.
Executive-Level Security Accountability
C-suite executives are prime targets for sophisticated attacks like spear phishing and whaling. Ensure executive leadership receives dedicated, role-specific training. Consider appointing a Chief Information Security Officer (CISO) or fractional CISO if you don’t already have dedicated security leadership.
Implement Strong Data Protection & Encryption Policies

Data is the asset attackers want most. Whether it’s customer payment information, employee records, or proprietary business intelligence — protecting that data through encryption and sound data management policies is fundamental to your security posture.
Encrypt Sensitive Customer Data
Any data that could identify customers, contain financial information, or expose health records must be encrypted — at rest, in transit, and ideally, in use (via technologies like homomorphic encryption for the most sensitive use cases). Implement end-to-end encryption for all customer-facing communications.
Data Classification Policies
Not all data carries the same risk. Establish a data classification framework with categories like Public, Internal, Confidential, and Restricted. Apply security controls proportionate to the sensitivity level of each data class. This prevents both under-protecting critical data and over-engineering controls for low-risk information.
Secure Data Storage Practices
Store sensitive data only where it needs to be. Regularly audit where critical data lives, who has access to it, and whether that access is still required. Implement data retention policies to securely delete data that is no longer needed — stored data you don’t manage is a liability.
GDPR & Compliance Alignment
If your business handles data belonging to EU residents, GDPR compliance is legally mandatory. But even outside the EU, frameworks like CCPA, PIPEDA, and sector-specific regulations (HIPAA for healthcare, PCI DSS for payments) impose strict data protection requirements. Aligning your encryption and data policies with these frameworks both reduces legal risk and generally improves security outcomes.
Regular Security Audits & Vulnerability Assessments
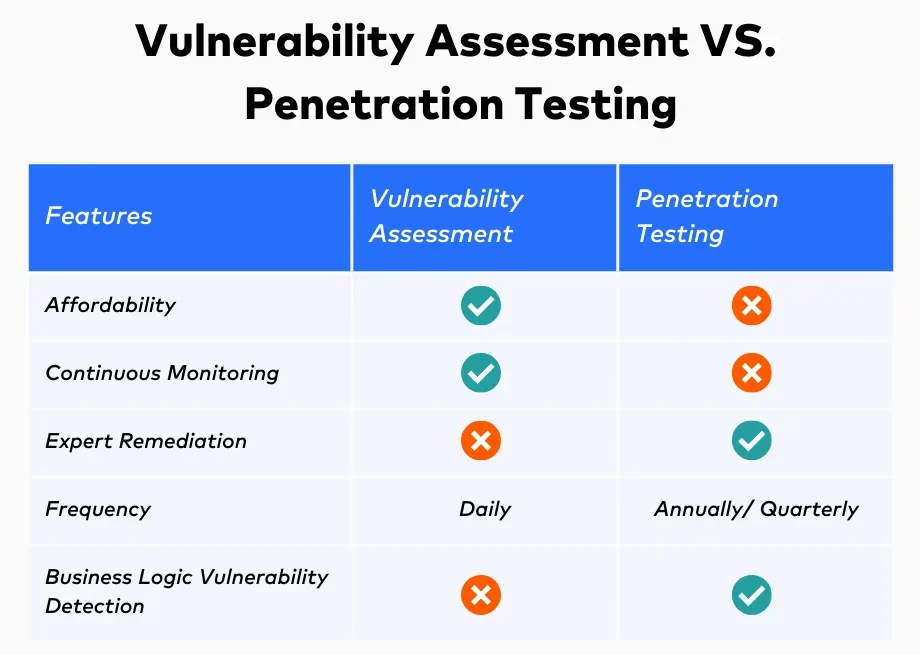
You cannot protect what you don’t know is vulnerable. Regular security audits and vulnerability assessments give you a clear-eyed view of your attack surface — and the opportunity to close gaps before attackers find them.
Penetration Testing
Penetration testing (ethical hacking) involves security professionals attempting to breach your systems using the same techniques real attackers would use — but in a controlled, authorized environment. Annual penetration tests at a minimum, with more frequent testing after major changes to your infrastructure, are best practice in 2026.
Automated Vulnerability Scanning
Between penetration tests, automated scanning tools continuously check your systems, applications, and network configurations for known vulnerabilities. Tools like Tenable Nessus, Qualys, and Rapid7 InsightVM can scan thousands of assets and prioritize remediation by risk level.
Patch Management Process
Unpatched software is one of the most exploited attack vectors. Implement a structured patch management process: inventory all assets, subscribe to vendor security advisories, prioritize critical and high-severity patches, and establish SLAs for patching (e.g., critical patches applied within 24 hours, high-severity within 72 hours).
Third-Party Risk Assessments
Your security is only as strong as your weakest vendor. Conduct security assessments of all third-party vendors and partners who have access to your systems or data. Use questionnaires, SOC 2 reports, and contractual security requirements to ensure your supply chain meets your security standards.
Incident Response & Business Continuity Planning
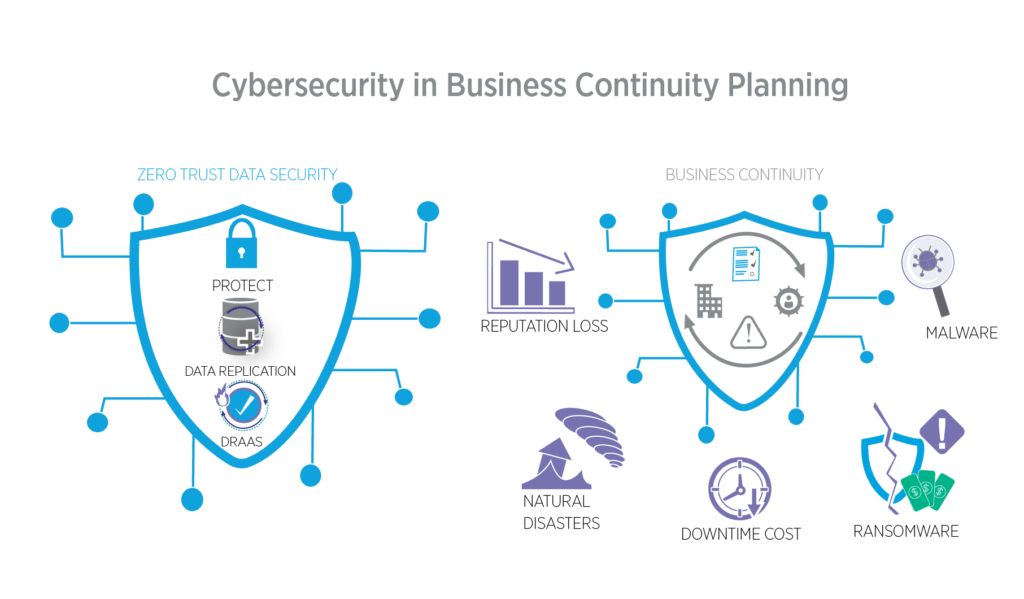
No security program can guarantee zero breaches. What separates resilient businesses from catastrophic failures is how quickly and effectively they can detect, contain, and recover from incidents. Having a tested incident response plan before you need it is not optional — it’s essential.
Step-by-Step Incident Response Plan
A robust IR plan follows six phases:
- Preparation: Define roles, tools, communication protocols, and runbooks before any incident occurs.
- Detection & Analysis: Identify that an incident has occurred, gather evidence, and determine scope and severity.
- Containment: Isolate affected systems to prevent further spread. Short-term containment (disconnect) followed by long-term (clean and restore).
- Eradication: Remove the root cause — malware, compromised credentials, vulnerable software — from your environment.
- Recovery: Restore systems to normal operations from clean backups, with enhanced monitoring.
- Post-Incident Review: Conduct a blameless retrospective to understand what happened, why, and how to prevent recurrence.
Assigning Roles & Responsibilities
Every IR plan must define who does what during an incident: Who is the incident commander? Who communicates with the media? Who notifies affected customers or regulators? Ambiguity during a crisis costs time — and time costs money.
Recovery Time Objective (RTO) & Recovery Point Objective (RPO)
RTO defines how quickly systems must be back online after an incident. RPO defines how much data loss is acceptable (measured in time). Align your backup frequency and disaster recovery infrastructure to meet your RTO and RPO targets. For most businesses, an RTO of 4 hours or less and RPO of 1 hour or less is the goal in 2026.
Compliance & Regulatory Requirements in 2026

The regulatory landscape for cybersecurity and data privacy has never been more complex — or more consequential. In 2026, compliance is not just a legal obligation; it is increasingly a competitive differentiator. Customers and enterprise clients want to work with businesses they can trust with their data.
Industry-Specific Compliance
Different industries face distinct regulatory requirements. Healthcare organizations must comply with HIPAA (US) and its international equivalents, which mandate strict controls over Protected Health Information (PHI). Financial services firms face PCI DSS for payment card data, SOX for financial reporting integrity, and regional regulations like DORA in the EU. E-commerce businesses handling consumer data must navigate GDPR, CCPA, and emerging state-level privacy laws.
Data Privacy Regulations
The General Data Protection Regulation (GDPR) remains the global gold standard for data privacy, but the landscape has expanded dramatically. In 2026, over 130 countries have enacted comprehensive data privacy legislation. Understand which laws apply to your business based on where your customers are located — not just where you are incorporated.
Documentation & Audit Trails
Compliance is not just about doing the right things — it’s about proving you did them. Maintain comprehensive audit logs, data processing records, security policy documentation, and evidence of training. Regulators increasingly expect organizations to demonstrate their security posture, not just assert it.
Consequences of Non-Compliance
GDPR fines can reach €20 million or 4% of global annual revenue — whichever is higher. Beyond fines, non-compliance can result in mandatory audits, business restrictions, reputational damage, and in severe cases, criminal liability for executives. Proactive compliance is far less costly than reactive remediation after a regulatory action.
Emerging Technologies in Business Cybersecurity

The same technological advances that empower attackers are also transforming defense. In 2026, AI, automation, and behavioral analytics are no longer cutting-edge luxuries — they are fast becoming baseline requirements for effective security at scale.
AI-Powered Threat Detection
Modern Security Information and Event Management (SIEM) platforms and Extended Detection and Response (XDR) solutions use machine learning to analyze billions of security events in real time, identifying patterns and anomalies that no human team could detect manually. Microsoft Sentinel, Splunk, and Exabeam are leading this space. AI dramatically reduces mean time to detect (MTTD) and mean time to respond (MTTR) to threats.
Security Orchestration & Automation (SOAR)
SOAR platforms automate repetitive security tasks — triaging alerts, enriching threat intelligence, and executing pre-approved response playbooks — freeing your security team to focus on complex investigations. In environments flooded with thousands of alerts daily, automation is not a luxury but a necessity.
Behavioral Analytics
User and Entity Behavior Analytics (UEBA) establishes a baseline of normal behavior for every user and system in your environment. Deviations — like an employee downloading 10,000 files at 2 AM or logging in from two continents within an hour — trigger alerts even when no known malware signature is present. This is particularly powerful for detecting insider threats and compromised accounts.
Quantum Computing Risks
Quantum computing presents a future existential threat to current encryption standards. Quantum computers capable of breaking RSA and ECC encryption may emerge within the next decade. In 2026, forward-thinking organizations are beginning to inventory their cryptographic assets and plan migrations to quantum-resistant (post-quantum) cryptographic algorithms, as standardized by NIST. Start preparing now — the transition will take years.
Conclusion: Building a Resilient Cybersecurity Strategy for 2026

Cybersecurity in 2026 is not a problem you solve once and forget. It is an ongoing discipline — a continuous process of assessing threats, strengthening controls, training people, and learning from every incident. The businesses that thrive in this environment are not necessarily those with the largest security budgets, but those with the most intentional and consistent approach to protection.
The pillars covered in this guide — Zero Trust architecture, robust IAM, cloud security, ransomware and phishing defense, employee training, data protection, regular audits, incident response planning, compliance, and AI-powered tools — form the foundation of a resilient cybersecurity strategy. No single measure is sufficient on its own. Security is a system, and every layer matters.
Start with your most critical gaps. Prioritize based on risk. Build incrementally. And above all, treat cybersecurity not as a cost center but as a strategic investment in your business’s continuity, reputation, and trustworthiness. The threats in 2026 are real — but so are the tools and strategies available to defend against them.
Ready to strengthen your security posture? Explore GizStreet’s curated cybersecurity tools, software reviews, and expert guides at gizstreet.com
Frequently Asked Questions (FAQs)
Q: What are the top cybersecurity threats for businesses in 2026?
A: The most significant threats in 2026 include AI-powered phishing and deepfake fraud, Ransomware-as-a-Service (RaaS), cloud misconfigurations, supply chain attacks, and insider threats. These attacks are more automated, targeted, and difficult to detect than ever before, making layered defenses essential.
Q: How can small businesses improve cybersecurity on a budget?
A: Small businesses can make significant security gains without enterprise budgets by prioritizing high-impact, low-cost measures: enabling MFA on all accounts (often free), using a password manager, deploying free or low-cost email filtering, training employees to recognize phishing, and maintaining regular cloud backups. Many cloud providers also include robust built-in security features at no additional cost.
Q: What is Zero Trust security and why is it important?
A: Zero Trust is a security framework based on the principle of ‘never trust, always verify.’ Rather than assuming that anything inside your network is safe, every access request is authenticated, authorized, and continuously validated regardless of location. It’s critical in 2026 because the traditional network perimeter no longer exists — employees work remotely, data lives in the cloud, and attackers can operate from inside compromised accounts.
Q: How often should businesses conduct security audits?
A: At minimum, businesses should conduct a comprehensive security audit annually. However, best practice in 2026 calls for continuous automated vulnerability scanning, quarterly access reviews, and penetration testing after any major infrastructure change or at least twice per year. High-risk industries (finance, healthcare) should consider even more frequent assessments.
Q: What is the best defense against ransomware attacks?
A: The most effective ransomware defense combines multiple layers: immutable offline backups (tested regularly), advanced email filtering and EDR software, employee phishing training, network segmentation to limit lateral movement, and a documented incident response plan. No single control eliminates the risk — defense in depth is the only reliable approach.
Q: Is cloud storage safe for business data?
A: Cloud storage from reputable providers is generally very secure at the infrastructure level — but security is a shared responsibility. Businesses must configure access controls correctly, enable encryption, enforce MFA, monitor for anomalous access, and understand what the provider secures versus what you must secure yourself. Misconfiguration, not provider failure, is the leading cause of cloud data breaches.
Q: How do businesses create an effective incident response plan?
A: An effective IR plan starts with preparation before any incident occurs: define roles and responsibilities, document response playbooks for common scenarios, establish communication protocols, and test the plan through tabletop exercises. The plan should cover the full incident lifecycle — detection, containment, eradication, recovery, and post-incident review. Review and update it at least annually and after any significant incident.
© 2026 GizStreet.com | All Rights Reserved
This article is for informational purposes only. Consult a qualified cybersecurity professional for advice specific to your business.