Home / Tablet Security Best Practices: Protecting Your Device and Data on the Go
Tablet Security Best Practices: Protecting Your Device and Data on the Go
sarankk | March 24, 2025 | 8 min read

Table of Contents
Introduction: Why Tablet Security Matters
In today’s increasingly mobile world, tablets have become essential tools for both personal and professional use. From browsing social media and streaming content to accessing sensitive work documents and making financial transactions, these versatile devices store a wealth of personal information. Yet, many users overlook the importance of securing their tablets against potential threats.
According to a 2023 Verizon Mobile Security Index report, 45% of organizations sacrificed mobile security in the name of expediency, and tablets were among the most vulnerable devices. This oversight can lead to devastating consequences, including data breaches, identity theft, and financial loss.
Let’s dive into comprehensive tablet security best practices that will help you protect your device and valuable data whether you’re at home or on the go.
Essential Tablet Security Measures
1. Keep Your Operating System and Apps Updated

One of the simplest yet most effective tablet security measures is keeping your operating system and applications updated. Software updates often include patches for security vulnerabilities that could otherwise be exploited by cybercriminals.
- Enable automatic updates whenever possible
- Check for updates regularly if automatic updates aren’t available
- Don’t postpone important security updates
- Remove apps you no longer use to reduce potential security risks
A 2024 Google security report revealed that devices running outdated operating systems were three times more likely to experience a security breach compared to those with the latest updates installed.
2. Implement Strong Authentication Methods
Protecting access to your tablet is your first line of defense against unauthorized users. Modern tablets offer multiple authentication options:
- Strong passwords/passcodes: Use a combination of uppercase and lowercase letters, numbers, and special characters
- Biometric security: Leverage fingerprint sensors and facial recognition when available
- Two-factor authentication (2FA): Enable 2FA for critical accounts and services
- Pattern locks: If using pattern locks, create complex patterns and avoid obvious shapes
According to cybersecurity firm McAfee, approximately 30% of tablet users still rely on simple 4-digit PINs or no security measures at all, making their devices extremely vulnerable to unauthorized access.
3. Encrypt Your Data

Encryption converts your data into a code that can only be deciphered with the correct encryption key, ensuring that even if your device falls into the wrong hands, your information remains protected.
Most modern tablets offer built-in encryption options:
- For iPads: Encryption is automatically enabled when you set up a passcode
- For Android tablets: Navigate to Settings > Security > Encryption & Credentials
- For Windows tablets: Use BitLocker or device encryption features
The importance of encryption cannot be overstated, especially for those who store sensitive personal or business information on their tablets. A 2023 study by the Ponemon Institute found that encrypted devices reduced the average cost of a data breach by nearly 30%.
Securing Your Tablet on Public Networks
4. Use a VPN for Public Wi-Fi

Public Wi-Fi networks present significant security risks due to their often limited security measures. When connecting to public Wi-Fi:
- Always use a reputable Virtual Private Network (VPN) service
- Avoid accessing sensitive information (banking, healthcare) on public networks
- Disable auto-connect features for public networks
- Verify network names before connecting to avoid “evil twin” hotspots
“Public Wi-Fi networks are the digital equivalent of speaking in a crowded room – anyone could be listening,” notes Eva Galperin, Director of Cybersecurity at the Electronic Frontier Foundation. “A VPN creates a private tunnel for your data.”
Some reliable VPN options include NordVPN, ExpressVPN, and Surfshark, which offer dedicated apps for various tablet operating systems.
5. Be Cautious with Bluetooth Connectivity
While Bluetooth is convenient for connecting peripherals and sharing data, it can also be a security vulnerability:
- Turn off Bluetooth when not in use
- Make your device “non-discoverable” when Bluetooth is enabled
- Be wary of unexpected pairing requests
- Regularly review and remove unnecessary paired devices
A 2023 security analysis by Kaspersky identified over 12 new Bluetooth vulnerabilities that affected various tablet models, highlighting the importance of cautious Bluetooth usage.
App and Content Security
6. Download Apps from Official Sources Only
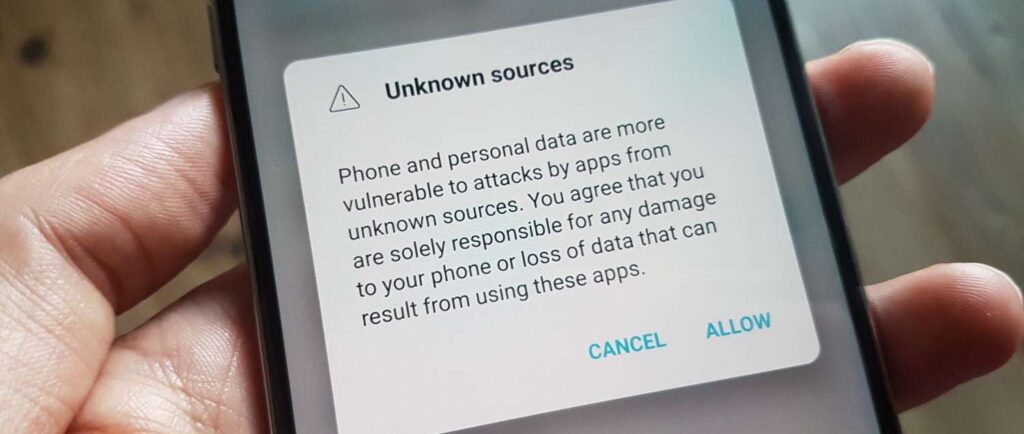
Malicious apps represent one of the most common threats to tablet security. To minimize this risk:
- Download apps exclusively from official sources (Apple App Store, Google Play Store)
- Research apps before downloading by checking reviews and developer reputation
- Pay attention to the permissions apps request during installation
- Use built-in security features like Google Play Protect or App Privacy Report on iOS
According to a 2024 report by Symantec, malicious apps were responsible for 67% of all mobile malware infections, with third-party app stores being the primary distribution channel.
7. Implement Parental Controls for Family Devices
For tablets shared with children:
- Set up age-appropriate content restrictions
- Control app installations and purchases
- Limit screen time and set usage schedules
- Monitor online activities while respecting privacy
Most tablet operating systems offer built-in parental control features, while additional apps like Norton Family, Qustodio, or FamilyTime provide enhanced monitoring capabilities.
Data Protection and Recovery
8. Backup Your Data Regularly

Regular backups ensure that even if your device is lost, stolen, or damaged, your data remains safe and recoverable:
- Use cloud backup services (iCloud, Google Drive, OneDrive)
- Consider local backups to a computer or external drive
- Verify your backups periodically to ensure they’re working properly
- Back up before major updates or changes to your device
The 3-2-1 backup strategy is recommended by data security experts: maintain 3 copies of important data, store them on 2 different types of media, with 1 copy stored off-site or in the cloud.
9. Enable Remote Tracking and Wiping
Most tablets offer built-in features to locate, lock, or erase your device remotely:
- For iPads: Enable Find My iPad
- For Android tablets: Set up Find My Device
- For Windows tablets: Activate Find My Device
These features can be invaluable if your tablet is lost or stolen. According to a 2023 Kensington study, 70 million smartphones and tablets are lost each year, with only 7% recovered. Remote wiping capabilities ensure your data doesn’t fall into the wrong hands.
Advanced Security Practices
10. Consider Security Software

While tablets generally face fewer malware threats than computers, security software can provide additional protection:
- Antivirus/anti-malware protection
- Privacy scanners that check app permissions
- Wi-Fi network security verification
- Anti-theft features
Reputable options include Bitdefender Mobile Security, Norton Mobile Security, and Malwarebytes for Mobile, which offer comprehensive protection without significantly impacting device performance.
11. Use Secure Browsers and Private Browsing
Your browsing habits can expose you to various online threats. Consider:
- Using privacy-focused browsers like Firefox Focus or Brave
- Enabling private browsing modes when appropriate
- Installing ad blockers and anti-tracking extensions
- Regularly clearing browsing data and cookies
A 2024 Mozilla Foundation study found that privacy-focused browsers reduced tracking attempts by up to 67% compared to standard browsers.
Physical Security Considerations
12. Never Leave Your Tablet Unattended

Physical security is often overlooked but remains crucial:
- Use tablet locks or security cases in public settings
- Keep your tablet within sight in public places
- Consider privacy screens to prevent visual hacking
- Store your tablet securely when not in use
“Visual hacking” – where sensitive information is viewed by unauthorized individuals looking over your shoulder – is surprisingly effective. A 2023 Ponemon Institute study demonstrated that 91% of visual hacking attempts were successful in public spaces.
Special Considerations for Business Use
13. Separate Work and Personal Use
For tablets used in professional settings:
- Use containerization or work profiles to separate personal and professional data
- Follow your organization’s security policies
- Consider Mobile Device Management (MDM) solutions
- Be especially cautious with work-related information
According to a 2024 IBM Security report, 60% of businesses reported data leaks related to improper handling of company information on personal or mixed-use mobile devices.
Staying Informed About Security Threats
14. Keep Educated About Current Threats

The digital security landscape evolves rapidly. Stay informed by:
- Following reputable tech news sources
- Subscribing to security bulletins from your device manufacturer
- Joining online communities focused on tablet security
- Considering basic cybersecurity courses
Resources like the National Cybersecurity Alliance, CISA’s security tips, and manufacturer security pages provide valuable, up-to-date information on emerging threats and best practices.
Conclusion: Creating a Security-First Mindset
Protecting your tablet and data requires a proactive approach. By implementing these tablet security best practices, you significantly reduce your risk of data breaches, identity theft, and other security incidents.
Remember that security is not a one-time setup but an ongoing process. Regularly review your security measures, update your knowledge, and adapt your practices as technology and threats evolve.
What security measures do you currently have in place for your tablet? Are there areas where you could strengthen your device’s protection? Taking action today can save you from potential headaches tomorrow.
References and Further Reading
- Verizon. (2023). Mobile Security Index Report. https://www.verizon.com/business/resources/reports/mobile-security-index/
- Google. (2024). Android Security & Privacy Year in Review. https://security.googleblog.com/
- Ponemon Institute. (2023). Cost of a Data Breach Report. https://www.ibm.com/security/data-breach
- Electronic Frontier Foundation. (2024). Surveillance Self-Defense Guide. https://ssd.eff.org/
- Kaspersky. (2023). Mobile Malware Evolution. https://securelist.com/mobile-malware-evolution-2023/106211/
- Symantec. (2024). Internet Security Threat Report. https://www.broadcom.com/support/security-center
- Kensington. (2023). IT Security & Laptop Theft Report. https://www.kensington.com/news/security-blog/
- Mozilla Foundation. (2024). Privacy Not Included Guide. https://foundation.mozilla.org/en/privacynotincluded/
- IBM Security. (2024). Cyber Resilient Organization Report. https://www.ibm.com/security/data-breach
- National Cybersecurity Alliance. (2024). Stay Safe Online Resources. https://staysafeonline.org/resources/
Last Updated: March 2025
best tablet security tips how to secure a tablet mobile device security for tablets protect your tablet secure mobile tablets secure tablet antivirus tablet data backup tablet data encryption tablet firewall configuration tablet firmware updates tablet hacking prevention tablet malware protection tablet network security tablet password protection tablet privacy settings tablet safe browsing tablet security apps Tablet security best practices tablet VPN setup


