Home / The Rise of Edge Computing & IoT Security (2026 Guide)
The Rise of Edge Computing & IoT Security (2026 Guide)
sarankk | March 2, 2026 | 6 min read
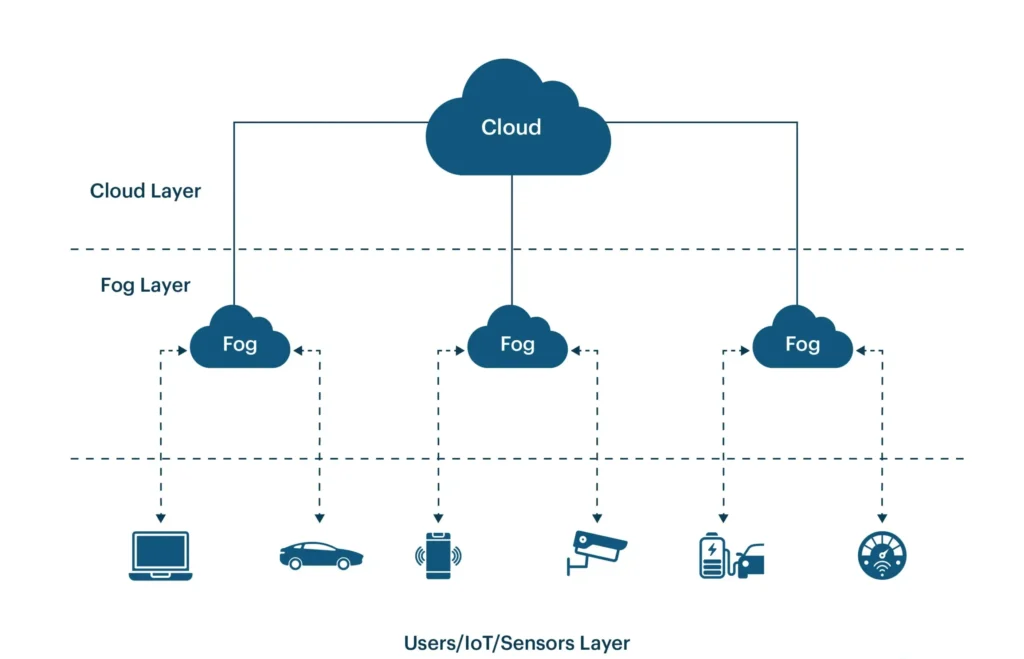
Table of Contents
The rapid expansion of connected devices is transforming the digital landscape. By 2026, billions of IoT devices—from smart home sensors to industrial monitoring systems—are generating massive volumes of real-time data. This explosive growth has created new opportunities for automation, analytics, and operational efficiency. However, it has also introduced significant IoT security challenges that businesses and governments can no longer ignore.
Traditional centralized cloud computing models struggle to handle the scale, speed, and latency requirements of modern IoT ecosystems. Sending every piece of data to a distant data center increases response times and exposes sensitive information to broader attack surfaces.
At the same time, cybercriminals are increasingly targeting IoT networks through botnets, firmware exploits, weak authentication, and distributed attacks. As a result, edge computing and IoT security are becoming deeply interconnected priorities.
Edge computing—processing data closer to where it is generated—offers a powerful solution. It reduces latency, improves performance, and enhances security by limiting exposure to centralized systems.
In this complete 2026 guide, we’ll explore what edge computing is, why IoT security is critical, major security risks, architectural strategies, best practices, real-world applications, and future trends shaping secure edge-driven ecosystems.
What is Edge Computing?
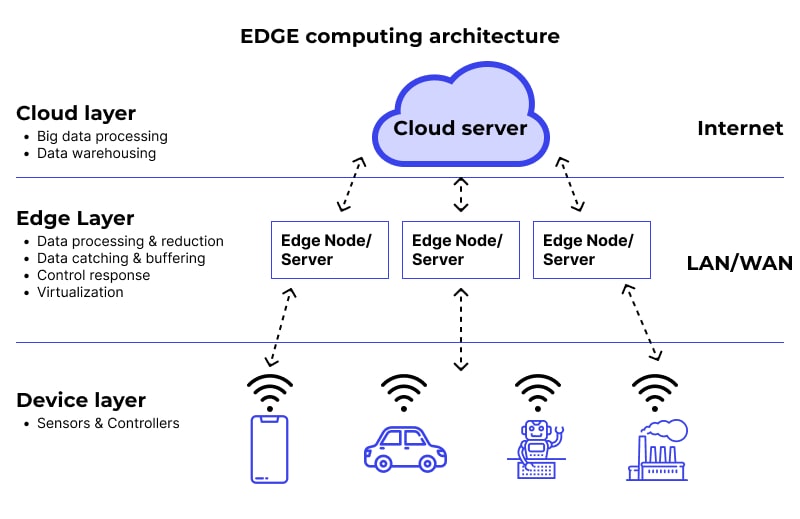
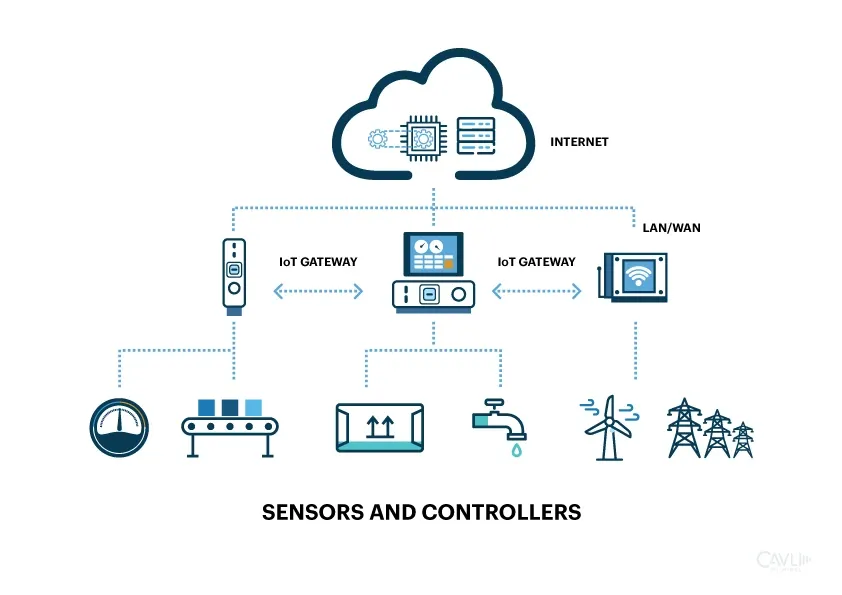
The edge computing definition refers to processing data closer to the source—near IoT devices, sensors, or users—rather than relying entirely on centralized cloud data centers.
In traditional cloud computing, data from devices is transmitted to distant servers for processing and analysis. In edge computing, local edge nodes (small data centers, gateways, or on-site servers) perform computation near the data source.
How Edge Differs from Traditional Cloud
- Cloud Model:Centralized processing
- Edge Model:Distributed processing
- Latency:Edge significantly reduces delay
- Bandwidth:Edge lowers network traffic
Real-Life Example
Consider smart traffic systems in a city. Traffic cameras collect data constantly. Instead of sending every video frame to the cloud, edge nodes analyze traffic patterns locally to adjust signals in real time. This reduces congestion instantly without waiting for cloud response.
In manufacturing, factory sensors monitor machinery health. Edge systems detect anomalies immediately, preventing costly downtime.
Why Edge Matters in 2026
With 5G connectivity, AI-powered analytics, and massive IoT expansion, edge computing supports ultra-low latency, bandwidth efficiency, and enhanced security—making it essential in 2026 and beyond.
What is IoT and Why is Security Critical?
The Internet of Things explained simply refers to physical devices connected to the internet that collect, transmit, and sometimes act upon data.
Examples include:
- Smart home thermostats and cameras
- Wearable health trackers
- Connected vehicles
- Industrial IoT (IIoT) sensors in factories
- Remote healthcare monitoring devices
Why IoT Increases Attack Surfaces
Every connected device becomes a potential entry point for cybercriminals. Many IoT devices are deployed rapidly without strong IoT device security controls.
Common risks include:
- Weak authentication systems
- Default passwords
- Unencrypted communication
- Outdated firmware
As organizations deploy thousands of connected devices, the attack surface expands exponentially. Without robust security frameworks, IoT ecosystems can become gateways for data breaches, ransomware, or operational sabotage.
How Edge Computing Supports IoT Infrastructure
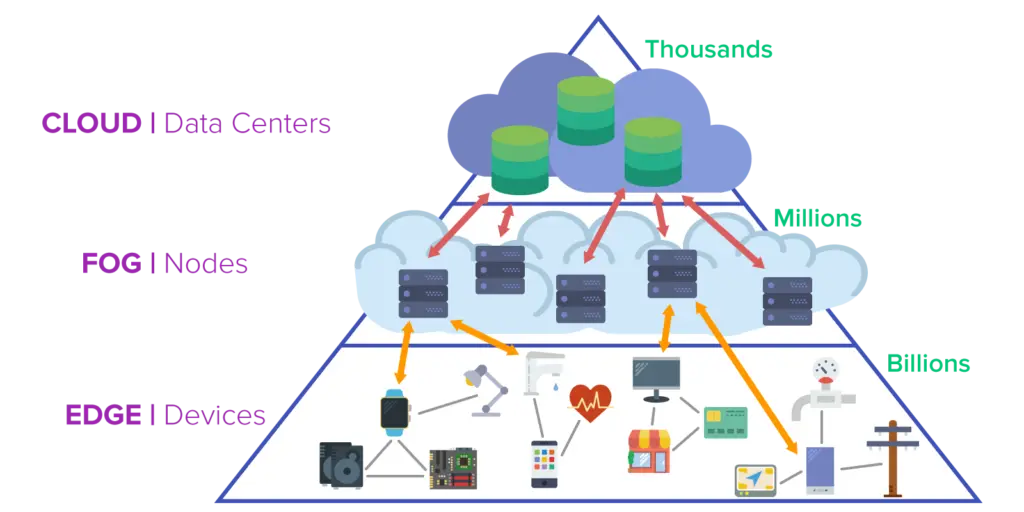
Edge computing for IoT enhances system efficiency and security through distributed processing.
Edge Nodes Explained
Edge nodes act as intermediaries between IoT devices and the cloud. They filter, process, and analyze data locally before sending only necessary information upstream.
Local Data Processing
By processing data at the edge, organizations reduce latency and enable real-time decision-making.
Reduced Bandwidth Usage
Instead of transmitting raw data continuously, edge devices send summarized or filtered results—lowering network congestion and costs.
Real-Time Analytics
Edge systems enable immediate analytics for applications like predictive maintenance or smart surveillance.
Why Edge Improves Performance
In IoT edge architecture, the simplified flow is:
IoT Device → Edge Node → Cloud Platform
This layered approach ensures rapid response times while still leveraging centralized cloud storage for long-term analytics.
Major IoT Security Challenges in 2026

IoT security risks continue to grow as adoption expands.
Weak Authentication Mechanisms
Default passwords and poor IoT authentication issues allow attackers easy access. Many IoT password vulnerabilities stem from unchanged factory credentials.
Unpatched Firmware & Updates
IoT firmware vulnerabilities arise when devices lack automated update mechanisms. IoT patch management remains challenging due to long device lifecycles and remote deployment locations.
Distributed Denial of Service (DDoS) Attacks
IoT DDoS attacks use compromised devices to form botnets. These botnet IoT threats can overwhelm servers or disrupt infrastructure.
Data Privacy Risks
IoT data privacy issues include unencrypted transmissions and excessive data collection. IoT data encryption is often overlooked in consumer-grade devices, increasing surveillance and breach risks.
How Edge Computing Improves IoT Security
Secure edge computing enhances IoT protection through multiple mechanisms.
Localized Data Filtering
Edge systems filter sensitive data before it reaches central servers, reducing exposure.
Reduced Cloud Exposure
By minimizing direct device-to-cloud communication, edge computing limits attack vectors.
Real-Time Threat Detection
Edge nodes equipped with AI analytics detect anomalies instantly.
Network Segmentation
Isolating IoT devices prevents lateral movement in case of compromise.
Encryption at the Edge
Encrypting data before transmission ensures confidentiality.
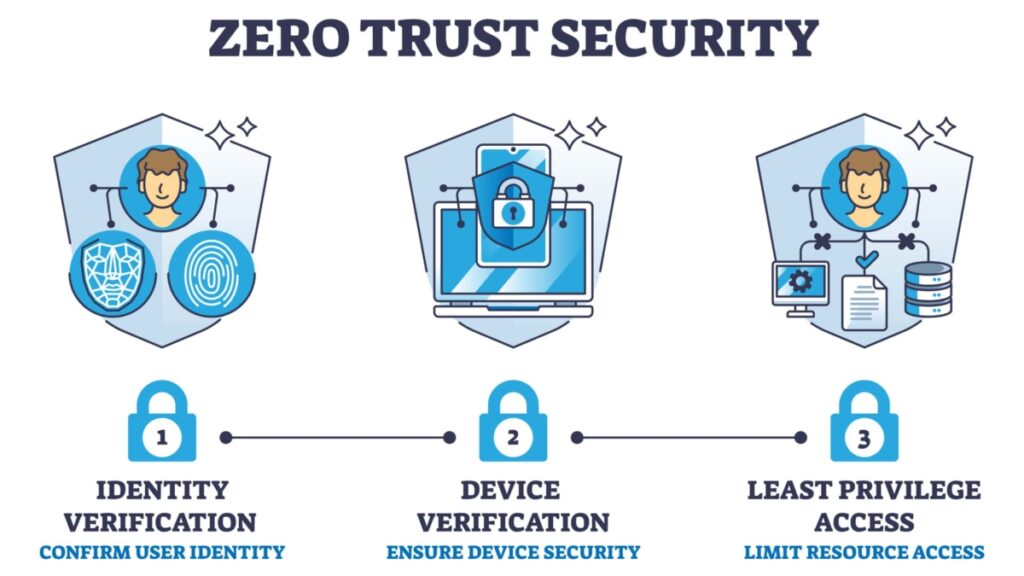
Zero Trust Implementation
Applying zero trust at the edge verifies every device and user continuously.
Real-World Example:
In a smart manufacturing plant, sensors monitor equipment. Edge systems detect abnormal temperature spikes and isolate affected devices immediately—preventing broader network compromise.
Best Practices for Securing Edge & IoT Systems
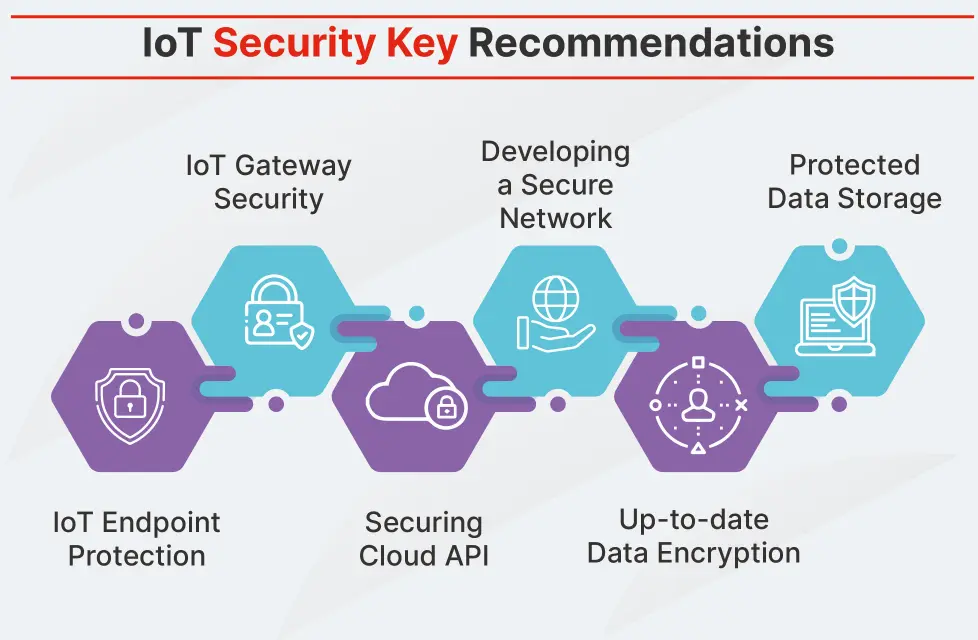
Strong Device Authentication
Implement multi-factor authentication IoT systems and device identity management frameworks.
End-to-End Encryption
Use IoT encryption standards such as TLS for IoT communication.
Regular Firmware Updates
Adopt IoT patch management strategy with automated updates IoT systems.
Network Segmentation
Design secure IoT architecture by isolating devices within segmented networks.
Practical implementation requires centralized visibility tools and automated monitoring platforms.
Real-World Applications of Edge & IoT Security

Smart Cities
Smart city IoT security ensures traffic systems and public infrastructure remain protected from disruption. Edge computing in smart cities supports real-time surveillance analysis.
Healthcare Monitoring Systems
IoT healthcare security protects remote patient monitoring security systems from breaches.
Industrial IoT (IIoT)
Industrial IoT security and IIoT cybersecurity prevent sabotage of manufacturing systems.
Future Trends in Edge Computing & IoT Security (2026 and Beyond)
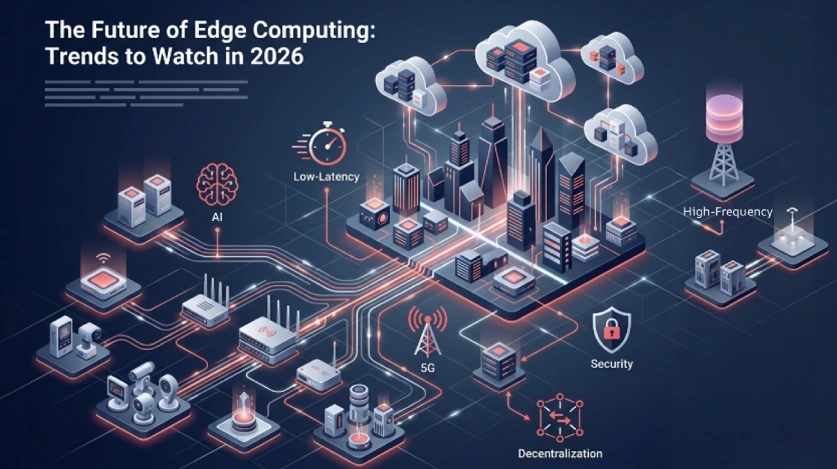
Future developments include:
- AI-powered edge analytics
- 5G ultra-low latency connectivity
- Decentralized security models
- Blockchain for IoT identity
- Expanding regulatory compliance requirements
The future of IoT security will rely on automation, distributed trust models, and privacy-by-design architecture
uctus nec ullamcorper mattis, pulvinar dapibus leo.
Conclusion: Building a Secure Edge-Driven Future

Edge computing and IoT security must evolve together. As connected devices multiply, centralized models alone cannot provide sufficient performance or protection.
By adopting secure edge computing strategies—combined with encryption, segmentation, authentication, and proactive monitoring—organizations can build resilient IoT ecosystems.
A layered, forward-thinking edge computing strategy ensures secure IoT infrastructure capable of supporting innovation well into the future.
FAQs
What is the difference between edge computing and cloud computing?
Edge processes data locally; cloud processes data centrally.
Why is IoT security becoming more important in 2026?
Because billions of devices expand the attack surface.
How does edge computing improve IoT security?
By reducing latency, filtering data locally, and limiting cloud exposure.
What are the biggest IoT security threats today?
Weak authentication, firmware vulnerabilities, botnets, and data leaks.
Can edge computing eliminate cloud security risks?
No, but it significantly reduces exposure and attack surfaces.
What industries benefit most from edge computing?
Smart cities, healthcare, manufacturing, and telecommunications.
How can businesses secure IoT devices effectively?
Implement strong authentication, encryption, segmentation, and continuous monitoring.