Home / Cybersecurity Trends 2026: Navigating the New Era of AI-Driven Threats and Quantum Risks
Cybersecurity Trends 2026: Navigating the New Era of AI-Driven Threats and Quantum Risks
swa | April 17, 2026 | 6 min read
Table of Contents
The digital landscape of 2026 isn’t just faster; it’s fundamentally more complex. Remember when a strong password and two-factor authentication (2FA) felt like an impenetrable fortress? Those days are officially in the rearview mirror. As we navigate through 2026, the intersection of Generative AI, quantum computing leaps, and hyper-connectivity has birthed a new breed of digital danger.
Staying informed about cybersecurity trends 2026 is no longer a luxury for IT professionals, it’s a survival manual for every internet user. From Deepfake-as-a-Service to autonomous malware that learns as it infects, the stakes have never been higher. But here is the silver lining: while the threats have evolved, so have our shields.
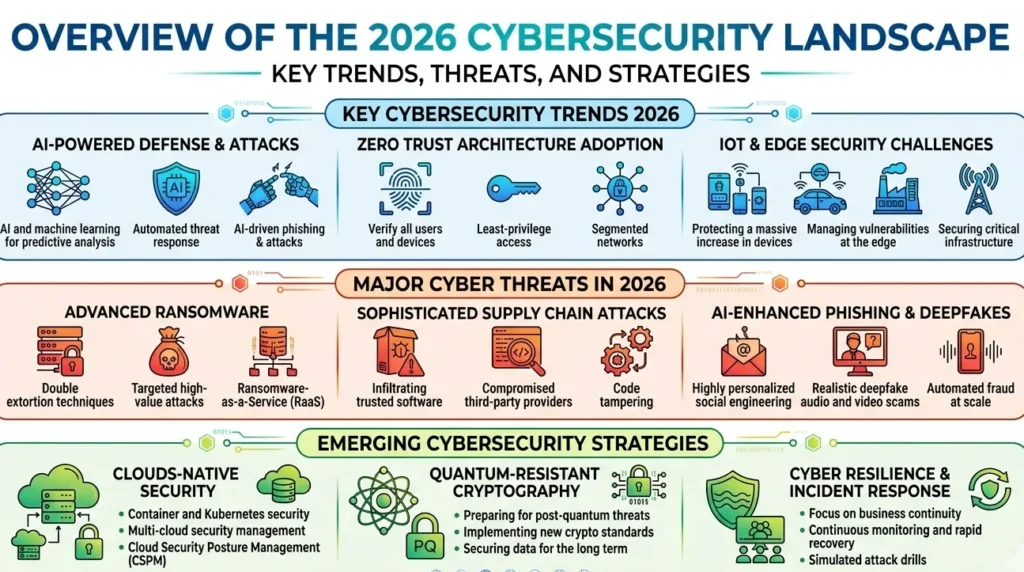
Why 2026 is a Turning Point?
As we look at the current data, the numbers are sobering. According to Statista, the global cost of cybercrime is projected to hit an eye-watering $12 trillion annually by the end of 2026. This isn’t just about stolen credit cards; it’s about systemic risks to power grids, healthcare systems, and the very concept of truth in a world of synthetic media.
The Rise of the Autonomous Hacker
In 2024 and 2025, we saw the script kiddies replaced by sophisticated AI agents. In 2026, these agents are fully autonomous. They can scan for vulnerabilities, craft bespoke phishing emails in 50 languages, and pivot through a network faster than a human analyst can hit refresh.
AI Security: The Double-Edged Sword
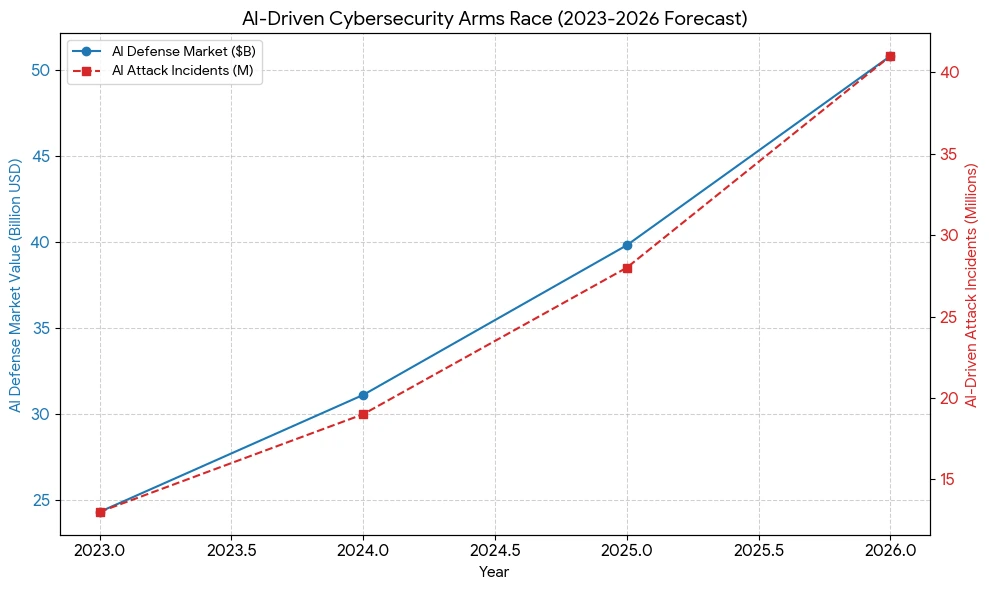
The most significant of all cybersecurity trends 2026 is the maturation of AI security. We are now living in a world of AI vs. AI.
Defensive AI: The New Guardian
Security Operations Centers (SOCs) are now powered by Large Language Models (LLMs) that don’t just alert humans to a breach, they predict it. Companies using AI-driven security tools have seen a 40% reduction in mean time to detect (MTTD), according to recent Gartner reports. These tools analyze behavioral patterns to spot impossible travel or unusual data exfiltration in milliseconds.
The Dark Side: Poisoning the Well
However, Adversarial Machine Learning has become a top-tier risk. Hackers are now focusing on Data Poisoning, corrupting the training data of a company’s AI to create blind spots. If you can trick the AI guardian into thinking a heist is just a routine update, the vault stays wide open.
Quantum-Resistant Cryptography: The Race Against Q-Day
While full-scale quantum computers capable of breaking RSA encryption might still be a few years off, the Harvest Now, Decrypt Later strategy is a massive threat in 2026.
What is Harvest Now, Decrypt Later?
Nation-state actors are currently stealing vast amounts of encrypted data, betting on the fact that they will have the quantum power to crack it by the end of the decade. Consequently, 2026 has seen a massive shift toward Post-Quantum Cryptography (PQC).
The Rise of Passkeys
Data privacy tools have shifted focus toward biometric decentralization.
Why Passkeys Won?
Passkeys, backed by the FIDO Alliance, use public-key cryptography to ensure that even if a server is breached, your credentials aren’t there to be stolen. Google, Apple, and Microsoft have made passkeys the default, leading to a 60% drop in successful phishing attacks among early adopters.
Hyper-Personalized Phishing & Deepfakes
Today’s cyber threats are surgical.
Social Engineering 3.0
Using leaked data from past breaches, AI can now generate a voice memo from your CEO or a video call from your CFO that is indistinguishable from reality. In 2025, a multinational firm lost $25 million because an employee was fooled by a deepfake video conference. In 2026, these tools are available to anyone for a $20 monthly subscription.
- Expert Insight: Trust but verify. Always use a safe word or an out-of-band communication channel for high-value transactions.
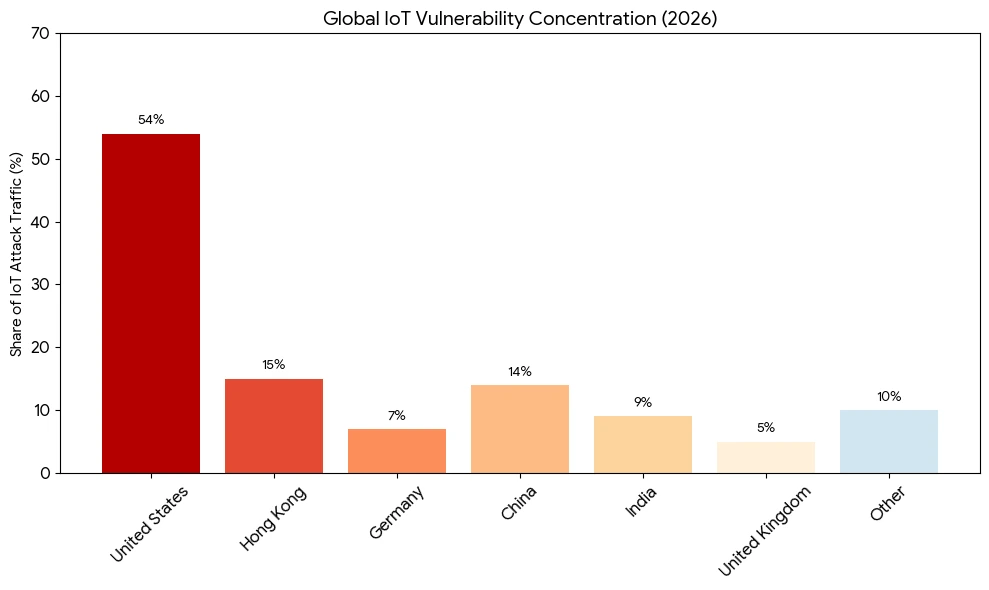
IoT and the Vulnerable Smart Home
By 2026, there are an estimated 30 billion connected devices globally. Your smart fridge, your EV charger, and even your connected lightbulbs are potential entry points.
The Shadow IoT Problem
The biggest risk isn’t the device itself, but the lack of updates. Many IoT manufacturers prioritize speed to market over long-term security patching. This has led to the rise of massive botnets that can launch DDoS attacks powerful enough to take down entire segments of the internet.
Identity Fabric and Zero Trust Architecture
In 2026, the perimeter is gone. Whether you are working from a cafe in Bali or the HQ in New York, the network treats you with the same level of suspicion. This is the essence of Zero Trust.
Continuous Authentication
Instead of a single login, cybersecurity trend 2026 emphasize continuous authentication. Your device’s location, your typing rhythm, and your gait (detected by mobile sensors) create a living identity. If the rhythm changes, the system locks down.
Privacy-Enhancing Technologies (PETs)
With global regulations like GDPR and CCPA evolving, data privacy tools have become more sophisticated.
- Homomorphic Encryption: Allows data to be processed while it’s still encrypted.
- Differential Privacy: Adds noise to datasets so that individual identities cannot be reverse-engineered.
How to Stay Protected Online in 2026: A Checklist
Staying safe doesn’t require a PhD in computer science. It requires a shift in habits.
- Audit Your AI Permissions: Check which apps have access to your Personal AI data.
- Use a Hardware Security Key:For your most sensitive accounts (Email, Banking), use a physical YubiKey.
- Segregate Your IoT: Put your smart home devices on a separate guest Wi-Fi network.
- Deepfake Awareness: Be skeptical of urgent video or audio requests for money, even from known contacts.

Conclusion: Resilience Over Paranoia
The cybersecurity trends 2026 highlight a clear reality: we cannot stop every attack, but we can make ourselves too expensive to target. By embracing AI security, utilizing modern data privacy tools, and maintaining a healthy dose of digital skepticism, you can navigate the 2026 landscape with confidence. The future is automated, but the defense remains human-centric.
FAQs
1. What are the biggest cyber threats in 2026?
The primary threats include AI-driven phishing, deepfake fraud, ransomware targeting critical infrastructure, and Data Poisoning of machine learning models.
2. How to stay safe online in this new era?
Switch to passkeys, use hardware security keys, keep all IoT devices on separate networks, and never trust urgent financial requests without secondary verification.
3. What is the role of AI in cybersecurity?
AI acts as both a sword and a shield. It helps hackers automate attacks, but it also allows defenders to detect and neutralize threats in real-time before they cause damage.
4. What are the best security tools for 2026?
Look for tools that offer Zero Trust Network Access (ZTNA), post-quantum encryption, and AI-powered behavioral analytics. Hardware keys like YubiKey remain the gold standard.
5. Why is cybersecurity more important now than ever?
As our physical and digital lives become inseparable from smart medical implants to autonomous vehicles, a cyber breach can now have direct physical consequences.